Quick Primer on SSH…
Here’s an oldie but goodie! I have to solve this problem of sharing sensitive information with other folks safely frequently. In our organization, we use not so much a really expensive cryptosystem as an internal system. That is, we’re a Microsoft ActiveDirectory shop so we get a CA for the cost of the server license and we use that to generate keys. From an email point of view, Exchange allows us to sign mail messages with the receiver’s public key and that seems to work well with the Government / DoD customers. So the real question seems to be if I wanted to setup secure communications with someone who was using just plain old hotmail or gmail. (That’s my take, at least.)
I think we see where this question is going: that’s right, we want to talk about PGP (“Pretty Good Privacy” and establishing a little Web of Trust. So let’s take that as read: we both pull down PGP, generate a keypair, and then we have to work out how we authoritatively setup the public key exchanges (since we don’t have a PKI). We can use the root server that Dr. Kabay listed to perform this exchange, and that’s the hard part (done!). From that point on, we sign / encrypt messages as per usual (sign with our private key, encrypt with the receiver’s public key) and we have our secure message transfer.
Let’s go one step further and say that I want to expose secure access to a system with someone external to my organization. To keep this in scope with the question, let’s say I want to setup a secure drop box we can exchange clever witticisms from (that’s communications of a sort, at least). Here’s how I’d do it (remember, this is all on Windoze, not *NIX):
- On my side, download Cygwin and install the OpenSSH package.Then use ssh-host-config to setup the sshd daemon and install it as a service. Run the sshd service (preferably on a non-standard port, but that will probably not be allowed by your firewall policy).
- Create a local account for the person I want to let in. Not a domain account, not a privileged account, just an account with minimal privileges but allowed to login (“Access this computer from the network†user right). Give that local account a very strong password (for example, Steve Gibson has a great generator you can use below). After all, this password will never be used directly.
- Use the mkpasswd -l | grep [local_user] >> /etc/passwd command to create a mapping between the account I want to grant access and the Cygwin pseudo-UNIX environment.
- Modify /etc/sshd_config to reference a nice, scary logon banner, specify the AllowUsers and set PasswordAuthenticate to “no.â€
- Tell my counterpart to download the complete Putty package (see below). Use puttygen to generate a strong keypair (say 2048 bits, SSH-2 RSA even though Dr. Kabay indicates RSA is not the latest).
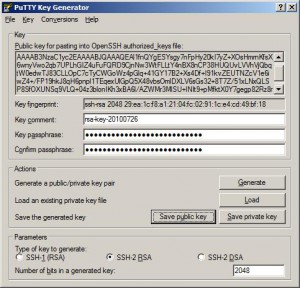
- Have my counterpart send me the public key from puttygen. That should occur out-of-band, but I’m thinking that we can do this pretty easily, I’ll have him encrypt the message with a secret key that we agree to on the phone.
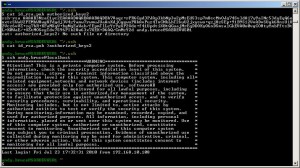
- On my new user’s home directory, create the requisite .ssh directory and cat the received public key into the authorized_keys2 file. Now the SSH daemon, when presented with my new user’s logon ID, will automatically challenge based on that key (that’s how we get the public key protection).
My new user can now logon to my SSH server using public key, and all for free! Have her use the Putty SCP (Secure CoPy) to be able to transfer files to our drop box (my new user has write privileges only to her local home directory, and read privileges for very little else).
Here’s a picture of my using (free!) public key support to login to my own box (localhost):
References:
“PGP Desktop Trial Software (Client Only)†– http://www.pgp.com/downloads/desktoptrial/desktoptrial2.html
“GNU + Cygnus + Windows = cygwin†– http://www.cygwin.com/
“Putty: a free telnet/ssh client†– http://www.chiark.greenend.org.uk/~sgtatham/putty/
“Perfect Passwords – GRC’s Ultra High Security Password Generator†– https://www.grc.com/passwords.htm. Steve Gibson is a legend in the PC security industry. Read his site, he’s got a lot of thought-provoking articles.
Leave a Reply