Solve “Unidentified Network Error” for Windows Server 2008
Anytime a non-routable network connection (any IPv4 network adapter that does *not* have a default gateway specified) is configured for a Windows Server 2008 server, the operating system will mark that network connection as an “Unidentified Network”. The downside? Windows Firewall kicks in by default unless you have changed the default policy to treat unidentified networks as private. This article discusses how to get rid of the Unidentified Network Error.
The Problem Space
Here is a picture of the problem in action. Even now in 2013, I still run into this problem occasionally upon reboots with Server 2008!
The problem with this “Unidentified Network” is that it affects the Windows Firewall settings. Server 2008 works by applying firewall rules to a network profile and this network profile is one of Domain, Public, or Private. Under the Windows Firewall, the rules for Domain and Private are relatively open: many network functions are allowed to support Active Directory or a trusted computer network scenario. The Public firewall rules, on the other hand, are very restrictive. So even though a computer may have a network interface that allows it to be a valid Active Directory domain member (as in the picture above with the “Management Network” that is part of the armycloud.cloud.army.mil Active Directory domain), Windows Server 2008 will apply the restrictive “Public†firewall rules because the computer also has at least one Public network; this is shown within the listed “iSCSI Fabric A” and “iSCSI Fabric B network interfaces.
“Hmmm” (with my ESP powers I can hear your thoughts!), “That Is Not a Good Thing. Losing iSCSI means Losing Storage Connectivity. That, in turn, means Downtime. We do *not like* Downtime!” And let me heartily second that opinion. So – given that in my case: a) I had to use Windows Server 2008; b) W2K8 Sucks in that this problem *will occur* every now and then; how to fix this problem??
A Workaround
Remember: The net effect of having an “Unidentified Network” under Windows Server 2008 is that the computer becomes largely non-functional in a trusted domain environment. Remote access, for example, is automatically turned off as is ping (ICMP) functionality. Aha! To work around this problem there are two strategies:
- Create a “fake” default route by pointing each unidentified network NIC to its own gateway and then using the
route -pcommand to ensure that the gateway is never used. There are blog entries on how to do this (see a technet blog I wrote years ago for one ). - Easier is to modify the local Group Policy so that “Unidentified Networks” are set to use the
Privateprofile; this has the effect of relaxing the Windows Firewall security rules.
In the case of my project, several systems have this scenario: the DataCore SANsymphony-V servers we use to present some legacy HP SANs to a SQL Server 2008 R2 cluster, and another NAS server that allows a physical SQL Server 2008 R2 standalone server to work directly from databases stored on a NAS powered by Windows Server 2008 and accessed via a private network (to ensure maximum network throughput). For each of these servers, the following procedure was applied:
- Open an elevated command prompt and type
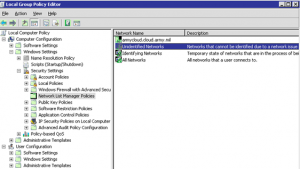
gpedit.msc. Then expand Computer Configuration -> Windows Settings -> Security Settings and click on the “Network List Manager Policies”. The screen displays as shown below:
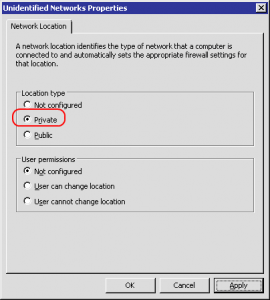
- Double-click on the “Unidentified Networks” setting on the right side of the screen:

- Change the “Location type†from “Not configured” to “Private”:
- Close the Group Policy Editor and, from the elevated command prompt, type
gpupdate /forceand verify that the computer policies are updated. The network connection should now display as aPrivatenetwork (although it will still be labeled as an “Unidentified network”):
Final Thoughts…
The above workaround is just that: a workaround. Just because I have been unable to determine why – at odd, rare intervals that seem to be correlate somewhat to Windows Updates – a functional Windows Server 2008 box will decide to “lose” its network definitions is a mystery. It is not a Domain issue because I have verified in at least one documented instance that I rebooted a Windows Server 2008 on a functional Active Directory domain as part of a whole series of serialized manual server patches and the problem occurred. A reboot seems always to “fix” the problem (that is: the network connection shows up as Domain) but I do not think it is simply a network hiccup. For example, I have an easily reproduceable error where Windows Server 2008 VMs simply refuse to stop cleanly from the guest and I must power them off from the VM control panel.
While I only have a very few Windows Server 2008 boxes left, I do not see them going away soon. (For example, an older NAS server I use simply won’t run under Server 2008 R2 as some of the proprietary drivers were apparently never updated.) So my effort here to workaround a disturbing network problem should not be taken as best practice.

Hi Andrew,
I’m so glad to finally find someone experiencing this issue, and at the same time I’m completely surprised that you have no replies prior to mine.
I have been looking all over the net for an explanation to this issue. Even though my issue may not be exactly as yours, it has the same side effects.
In my case I’m hosting a W2008 R2 running EXCH 2010 SP1.
My issue is the following:
Every time I have to reboot the router that’s serving as a gateway to this server, I loose Remote Desktop and the server goes into the unidentified network mode and DNS goes crazy about not finding any DC. (This is also a DC and GC) ALL-IN-ONE setup.
Fortunately those are the only 3 mayor things that happens. During that time e-mails still flowing and no Exchange functionality is lost. After a reboot everything goes back to normal.
This is a physical server. I have another W2008 R2 Virtual server, that DOESN’T experience this issue, despite being connected to the same router.
Your work around is interesting, but it is a bit different than yours.
Any comment or tip would be greatly appreciated.
Best regards!
Aliet
Aliet – What you are describing is different than my situation. My situation has to do with the fact that Windows will not assign a network type to a NIC without a gateway…but adding two “default” gateways leads to big problems. Hence my workaround.
What you are describing I also run into in my home lab. It is because a system is coming up when no route is available to an AD domain controller. Net result: machine can’t login to domain with the resulting network problems. The solution for that is redundancy.
Enable redundant network paths (two switches, two cards, etc.) and then the problem will be much rarer or simply never occur.
I think I have found the cause/solution for losing network card connection to “Domain Network” and switching to “Unknown Networkâ€
It happens usually after server reboot and almost always after server maintenance and, to my knowledge so far, only on W2008 and W2008R2 servers, regardless physical or virtual.
Reason: The Network Discovery is turned off!
Description: Network discovery is a network setting that affects whether your computer can find other computers and devices on the network…
ON settings: This state allows your computer to see other network computers and devices…
OFF settings: This state prevents your computer from seeing other network computers and devices…
Under “Control Panel\Network and Internet\Network and Sharing Center\Advanced sharing settingsâ€, for “Domain†profile the settings should be changed to “Turn ON network discoveryâ€
Network discovery requires that the:
– DNS Client,
– Function Discovery Resource Publication,
– SSDP Discovery, and
– UPnP Device Host
services are started, that network discovery is allowed to communicate through Windows Firewall, and that other firewalls are not interfering with network discovery.
Works for me…
Thanks very much for the note, Nash! Great that you found a solution and keep up your good work!
Greetings Gents,
Great info here. I am having issue were my server 2008 after reboot is flat out not saving the static ipv4 config. I have not noticed if the unidentified network issue has shown up or not but, I was thinking my issue may be similar. Any insight into this would be greatly appreciated. Thank you in advance!
Kris, I was having the same issue as you the static IP would not stay,I was able to ping from some clients and not from others, what turn out to be my problem was the network port on the Switch, as soon as I moved it to another port on the same switch or a different switch it worked if I put it back on the old port the problem came back.
Great fix!!
thank you.